Privacy and data protection in 2026
Want to build a comprehensive data protection and privacy strategy but unsure where to begin? Keep reading to boost your overall security and cybersecurity strategies.

Your organization generates large amounts of sensitive security information daily, from video feeds to access logs.
Simply put, there’s a lot of physical security data and information to protect.
The other challenge? The ever-present issue of cybercrime and evolving cybersecurity threats, not to mention new industry regulations like NIS2 and GDPR, make it critical for businesses to stay on top of their data protection and privacy strategy.
The bottom line? Robust security measures, advanced cybersecurity protocols, and strict privacy practices are essential for safeguarding valuable data.
Are you confident your physical security data is truly safe? Here’s what you need to know about implementing a strategy with privacy in mind.
GUIDE
DATA PRIVACY 101
Understanding the landscape
Did you know global cybercrime damage is predicted to cost the world $12.2 trillion by 2031? This surge means that a traditional privacy protection strategy might not be enough.
As threat actors become savvier, people demand more transparency in handling their data. New laws and evolving legislation also hold businesses to high cybersecurity and privacy standards, pushing them to strengthen their data security and safeguard sensitive information.
What does this mean for your organization? Here’s what to keep in mind:
-
When considering new security systems, look beyond just features and pricing
-
Investigate the vendor’s track record
-
Ask if they’ve faced breaches, regulatory fines, or issues with data protection
A history of cybersecurity gaps can indicate deeper issues with how they handle sensitive data protection and system integrity.
Trust is earned through proven transparency and commitment to security, not just marketing claims. An uncompromising privacy strategy can form the backbone of reliable and resilient security. That means you can’t just set and forget your hardening tools and privacy defenses.
With cybersecurity threats and new privacy regulations rising, compliance becomes a continuous process. Vigilance is key if you want to protect your data. To stay protected, it’s crucial to keep investing in data protection and privacy.
“As society is waking up to the kinds of disruption that immature cybersecurity can have on daily lives, governments around the world are implementing more directives and regulations. Unsurprisingly, this has made its way to the physical security industry, with the effect of increasing our attention to our overall security posture.”
Mathieu Chevalier, Manager and Principal Security Architect at Genetec
BLOG
DATA PRIVACY TIP 1
Start with a strategy
When was the last time you reviewed your data and information handling practices? It’s always good to consider:
-
Where your data is collected
-
How it’s stored
-
How long data is retained
-
Who has access
Ultimately, you might uncover gaps in your data and privacy policies that need fixing.
From there, you can implement new processes, adjust your privacy policies, and even educate your users about cybersecurity. We found that this was the #1 cybersecurity practice implemented by organizations worldwide to boost compliance with new or existing laws.
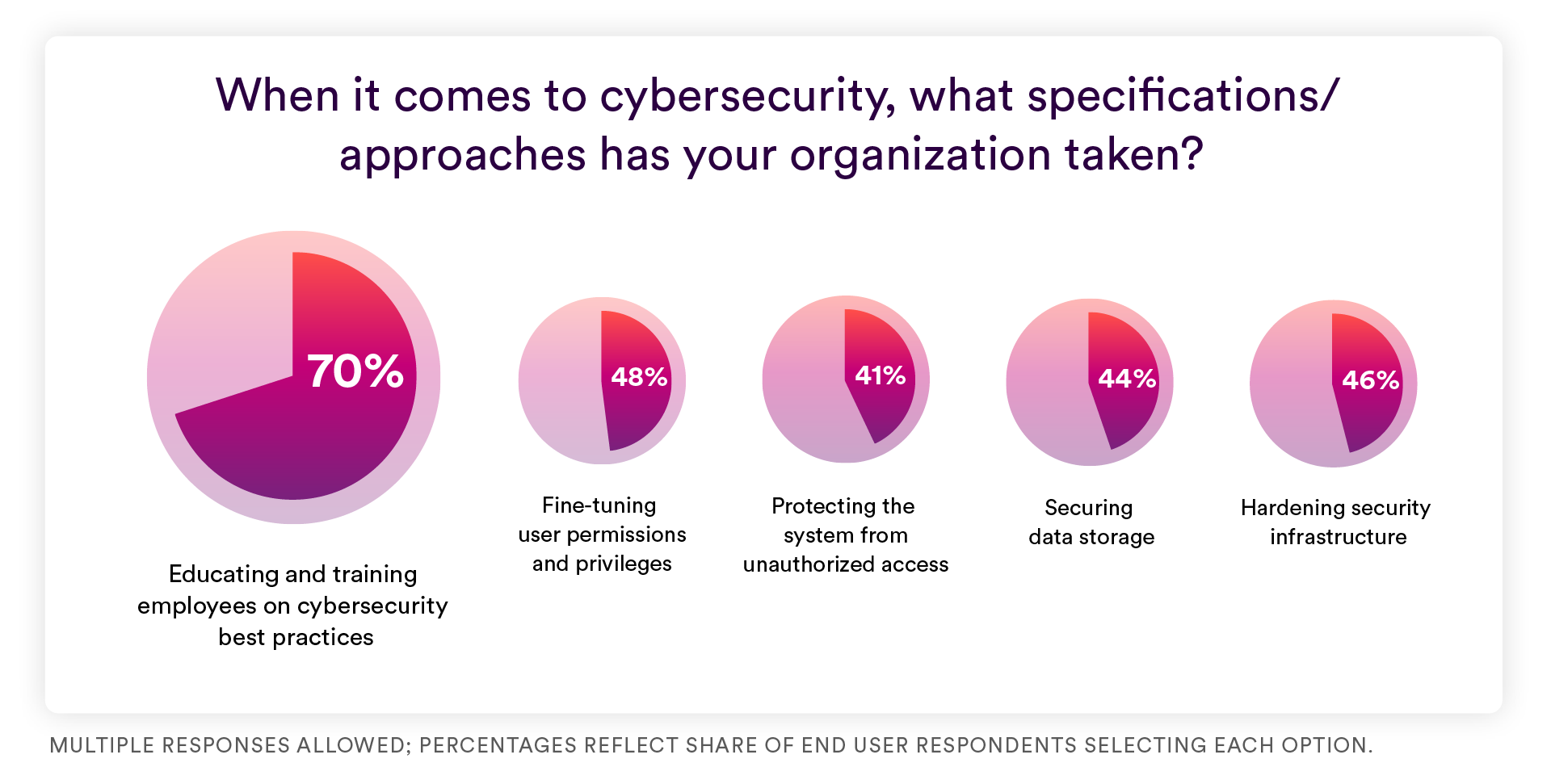
Source: 2026 State of Physical Security Report, Genetec Inc.
Remember, transparency is key when developing a robust data protection strategy. Share your ongoing data and privacy initiatives with your employees, customers, and the public. This builds trust and shows your commitment to keeping information and data secure.
DATA PRIVACY TIP 2
Implement strong defenses
Design your system with privacy at its core. You can do this by layering defenses throughout your physical security setup to help safeguard your information:
-
Encrypt all video and data during storage and transmission
-
Use built-in multi-factor authentication to strengthen cybersecurity
-
Manage user activity with detailed individual and group-based authorizations to ensure compliance
-
Automate video and data retention policies to delete sensitive data promptly
-
Deploy hardening tools that detect vulnerabilities and address new cybersecurity challenges
-
Apply automatic video anonymization to protect identities and privacy
-
Invest in a digital evidence management system for secure data sharing during investigations
BLUEPRINT
DATA PRIVACY TIP 3
Take it to the cloud
Cloud services give you an easier path to cyber resilience by offloading constant upkeep from your IT and security teams. A trusted cloud vendor’s dedicated experts work 24/7 to mitigate new vulnerabilities and keep your system hardened against threats. This enhances data security and fortifies your privacy and overall security infrastructure.

A physical security as a service (PSaaS) solution can also help, especially with compliance. This way, you’ll always have the latest software updates and new cybersecurity features. That includes everything from privacy controls and strong user authentication to system health monitoring tools, all without extra hassle for your team.
Your channel partners can also monitor your system’s health remotely. This allows their cybersecurity experts to spot further enhancement opportunities, such as new integrations, specialized training, and even customized measures.
Augmenting your system’s data security with cloud services can help build a resilient security posture.
REPORT
"Users are settling into defined cloud strategies, favoring hybrid models that balance scalability with the flexibility to keep specific workloads on-premises when needed. … Doing this enhances resilience, continuity, and control across both cloud-connected and local systems."
– Excerpt from the 2026 State of Physical Security Report
DATA PRIVACY TIP 4
Choose the right partner
Choosing a vendor that’s committed to privacy, cybersecurity, transparency, and compliance is crucial.
Whether you’re going for a cloud, on-premises, or hybrid solution, a reliable partner does more than provide robust privacy features. They adapt as new risks emerge and laws evolve, strengthening compliance, privacy, and data protection.
BLOG
A few more data privacy tips:
-
Find solutions you can trust: Look for cybersecurity certifications including ISO/IEC 27001 standard, ISO/IEC 27017 standard, SOC 2 Type II Compliance, and others.
-
Look for secure and reliable integrations: Consider the broader technology ecosystem and whether the vendor’s partners also value privacy and data protection.
-
Work with responsible artificial intelligence: Examine whether the vendor prioritizes privacy, data governance, transparency, safety, and human-led decision-making in AI development.
-
Always ask for transparency: Ask how the vendor handles vulnerability management, disclosing their privacy policies, and data protection practices under current laws.
