SORT BY

Data protection
When physical security goes to the cloud, data sovereignty matters
In Europe, data sovereignty is a major priority. What’s data sovereignty? It means you must follow the laws where your data is collected, stored, or processed. This matters as cloud adoption grows and security data multiplies.

Industry insights
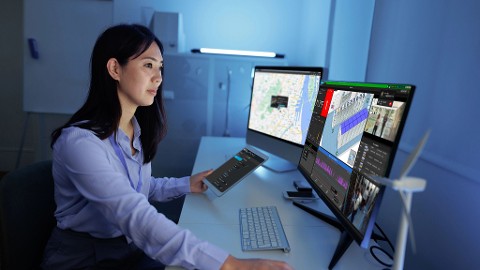
Physical security for IT: 5 essentials to look for
Information Technology (IT) teams play a critical role in physical security decisions. In this blog, you'll learn how physical security software and appliances can align with IT priorities—from cybersecurity and open architecture to flexible deployments and a unified platform.

Product
Q&A about evidence management at Galveston County
Genetec speaks with Kevin Petroff about implementing Genetec Clearance for prosecution discovery. In the Q&A, we learn how regulatory changes inspired the Galveston County DA’s Office to take a modern approach to managing and sharing evidence and how their discovery processes have improved today.

Product
High severity vulnerability affecting the Hardware Inventory Task of Security Center
A high severity vulnerability that can lead to a full compromise of the system hosting the SQL database was found in the Genetec Security Center product line. This vulnerability was discovered internally by the Genetec engineering team. There is currently no evidence of this vulnerability being exploited in the wild.